
Recently I wanted to run DC/OS on Packet, the bare metal cloud. However, the Terraform scripts do not setup any firewall rules. This leaves the cluster exposed to internet traffic. To fix this
I setup an IP whitelist to block undesirable external traffic. In this blog I will show you how this works using the ipset and iptables commands.
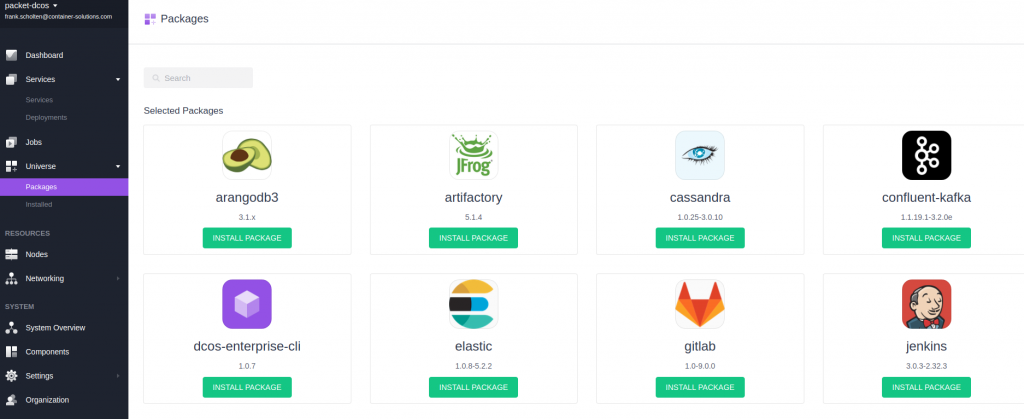
DC/OS on Packet
First let's create a small development DC/OS cluster. We will deploy this cluster on Packet, the bare metal cloud provider. In many cases Packet is cheaper with better performance than AWS and it offers bare-metal instances and a layer-3 network so it is an interesting option for running DC/OS on. To get started clone the repository with Terraform scripts for DC/OS on Packet and then follow the DC/OS Terraform documentation. I recommend creating a small cluster with a single master, a bootstrap node and a at least one agent.
IP whitelisting
The easiest way to protect the cluster is via an IP whitelist. This whitelist will be applied to all nodes in the cluster. This way we can create firewall rules that only allow traffic from your IP and the IPs of nodes in the cluster while logging and dropping other traffic from outside else. This setup should be good enough for a simple development cluster. On all instances create a whitelist that contains your laptop, workstation or company IP and the IPs of each node in the DC/OS cluster.
What is ipset?
You are probably familiar with iptables but may not know ipset. ipset is like iptables part of netfilter subsystem in Linux and it support creating lists of IPs or networks also supports IPv6. For more information check the ipset website. Before you create the IP whitelist SSH into your cluster nodes using the following command. Note the private key for Packet and the core user because the cluster runs CoreOS.
ssh -i packet-key core@$IP
Now let's create an IP whitelist:
- Create an IP whitelist with
ipset create whitelist hash:ip - Use
ipset add whitelist $IPto add an IP - Add IPs from the output of
terraform output - Add Google's DNS servers
8.8.8.8and8.8.4.4 - Add the loopback address
127.0.0.1 - Add the IPs from interfaces created by Spartan, Mesospheres DNS dispatcher
198.51.100.1,198.51.100.2,198.51.100.3
Setting up the firewall
Let's activate the whitelist with some remaining firewall rules. First, we will allow established and related connections. If you don't do this DC/OS won't be able to connect to the universe package repository. Second, let's log packets that are not in the whitelist and third, let's drop them. See the commands below.
ipset create whitelist hash:ip
ipset list whitelist
(out) Name: whitelist
(out) Type: hash:ip
(out) Revision: 4
(out) Header: family inet hashsize 1024 maxelem 65536
(out) Size in memory: 120
(out) References: 0
(out) Members:
ipset add whitelist $YOUR_IP_HERE
ipset add whitelist $MASTER_IP
ipset add whitelist $AGENT1_IP
ipset add whitelist $AGENT2_IP
ipset add whitelist $AGENT3_IP
ipset add whitelist 127.0.0.1
ipset add whitelist 198.51.100.1
ipset add whitelist 198.51.100.2
ipset add whitelist 198.51.100.3
ipset add whitelist 8.8.8.8
ipset add whitelist 8.8.4.4
iptables -A INPUT -m conntrack --ctstate ESTABLISHED,RELATED -j ACCEPT
iptables -A INPUT -m set ! --match-set whitelist src -j LOG
iptables -A INPUT -m set ! --match-set whitelist src -j DROP
Great! The cluster is ready and shielded from external internet traffic.
 DC/OS on Packet - The Bare Metal Cloud
DC/OS on Packet - The Bare Metal Cloud
Takeaways
We described a simple way to manually setup a firewall for a small development DC/OS cluster on Packet. An obvious improvement would be to make these rules persistent and to automate this process by using tools like Ansible or Nix or to install firewall management software.
Links
- DC/OS Website
- DC/OS Documentation
- Packet website
- ipset website
- Linux Journal article on ipset by Henry van Styn (@vanstyn)
Keep in touch!
Thanks for reading! Questions? Comment on the blog or talk us at @ContainerSoluti or to myself at @Frank_Scholten.
P.S. Like to learn more about Cloud Native?
Container Solutions offers Cloud Native Training Courses such as Kubernetes 101, Continuous Delivery with Docker, Container & Microservice Security, Monitoring with Prometheus and our 2-day From Zero to Hero Workshop. We also offer a month-long Cloud Native Bootcamp. The bootcamp will cover Linux Basics, Agile and TDD, containers, orchestrators and Design Thinking courses. The final week of the bootcamp consists of a Hackathon where you will build a Cloud Native application with your team. To learn more check out our training courses website.


 Previous article
Previous article
